Onboarding/Decentralization
A “consortium” is a business network comprised of a group of organizations and/or multiple members who have a shared business goal. A centralized consortia is owned and governed by a single entity, whereas a decentralized consortia has shared ownership across a group of stakeholders. All operations at this tier are off-chain and include cloud + region whitelisting, membership creation, certificate management, smart contract management, onboarding with optional RBAC governance, and network auditing.
Configuring your Consortium
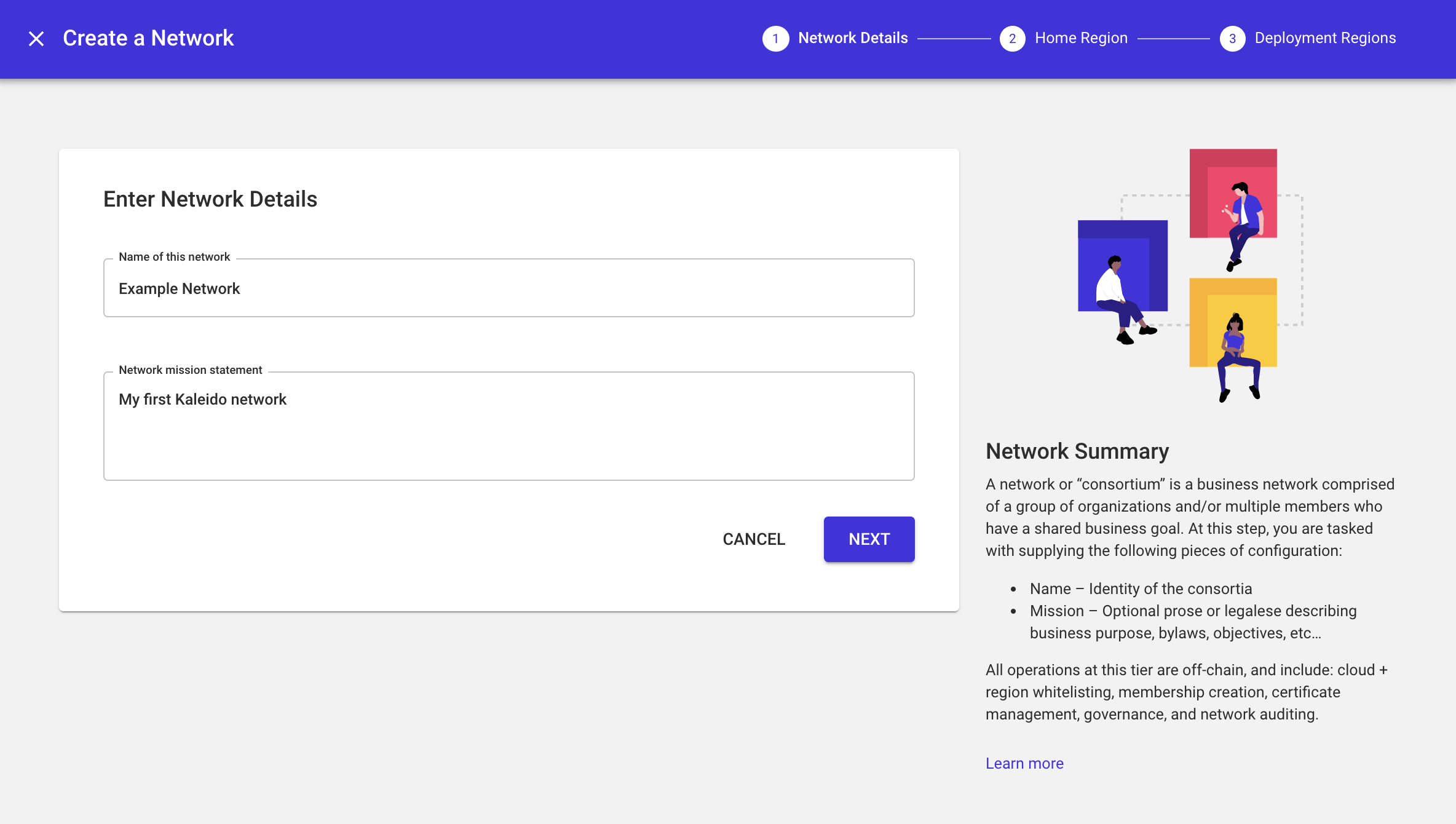
To establish a consortium in Kaleido, you will need to Create a Network. A consortium (or network) can be built across a single cloud provider, across multiple regions within a single cloud provider, or multiple cloud providers and a selection of underlying regions. When creating a consortium, you are tasked with supplying the following pieces of configuration:
- Name – Identity of the consortium
- Mission – Optional prose or legalese describing business purpose, bylaws, objectives, etc.…
- Home Region – Cloud provider and underlying region where consortium metadata (e.g., memberships) is stored. The available cloud providers are AWS and Microsoft Azure.
Clouds & Regions
A consortium can be configured to whitelist one or more regions across the two available cloud providers – AWS and Azure. Resources (nodes and services) can be created and deployed on any of the consortium’s whitelisted cloud regions and easily integrated with existing cloud suites and application stacks.
Decentralization
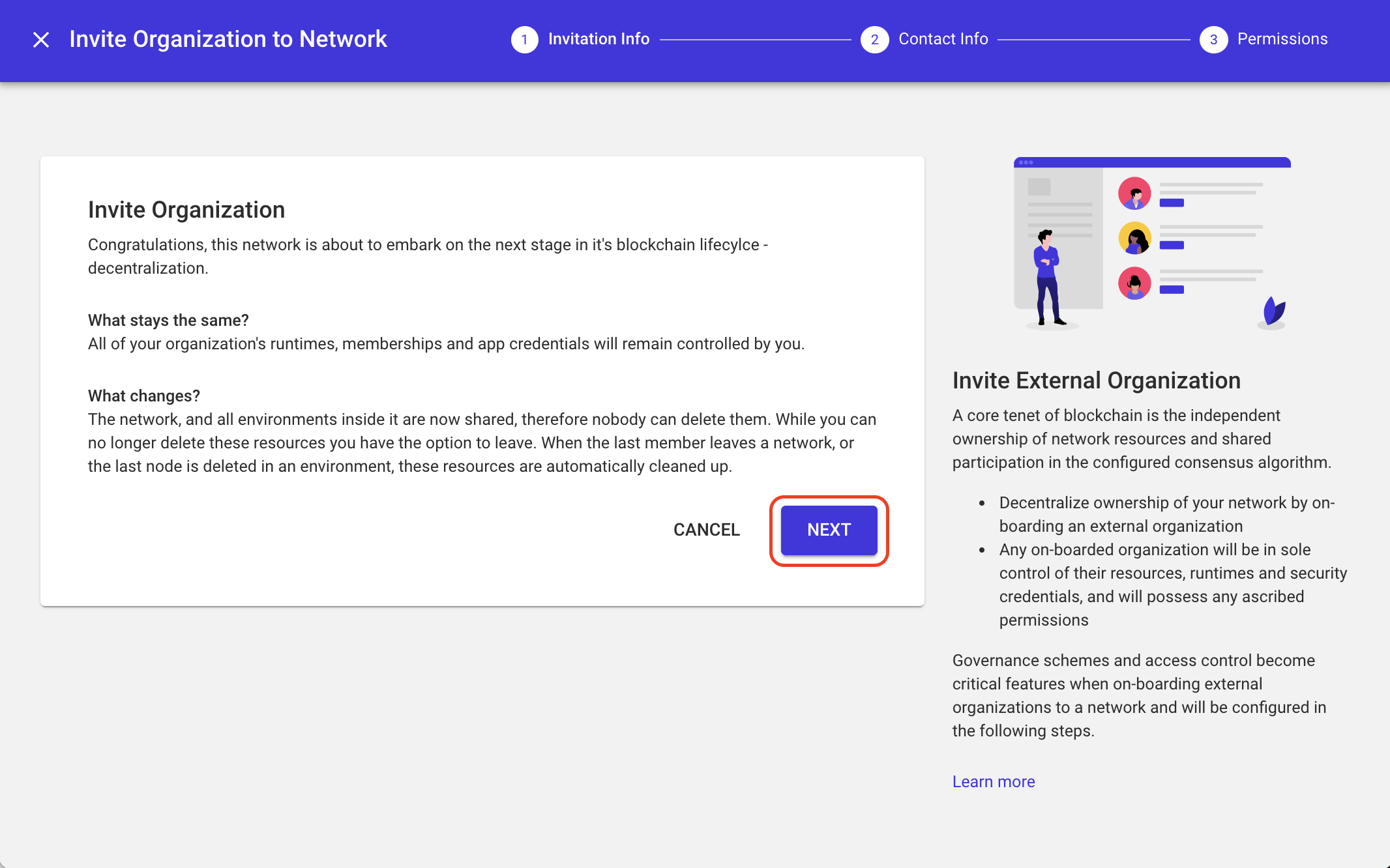
A core tenet of blockchain is the independent ownership of network resources and shared participation in the configured consensus algorithm. However, when operating within the scope of a consortium, there needs to be additional enforceable permissions beyond the ability to stand up resources. Business networks are diverse, and it’s atypical for every stakeholder to exist on equal footing. As such, governance schemes and access control become critical features when on-boarding external organizations to a consortium.
Modeling/Simulating a Business Network
When you first start using the Kaleido platform, and during PoC phases, you can model many participants in your consortium with new Memberships under a single administration/security domain.
Each Membership has a unique identity and application security credentials to access cloud resources. However, they are managed under the same Kaleido Organization and operated by the same organizational admin(s).
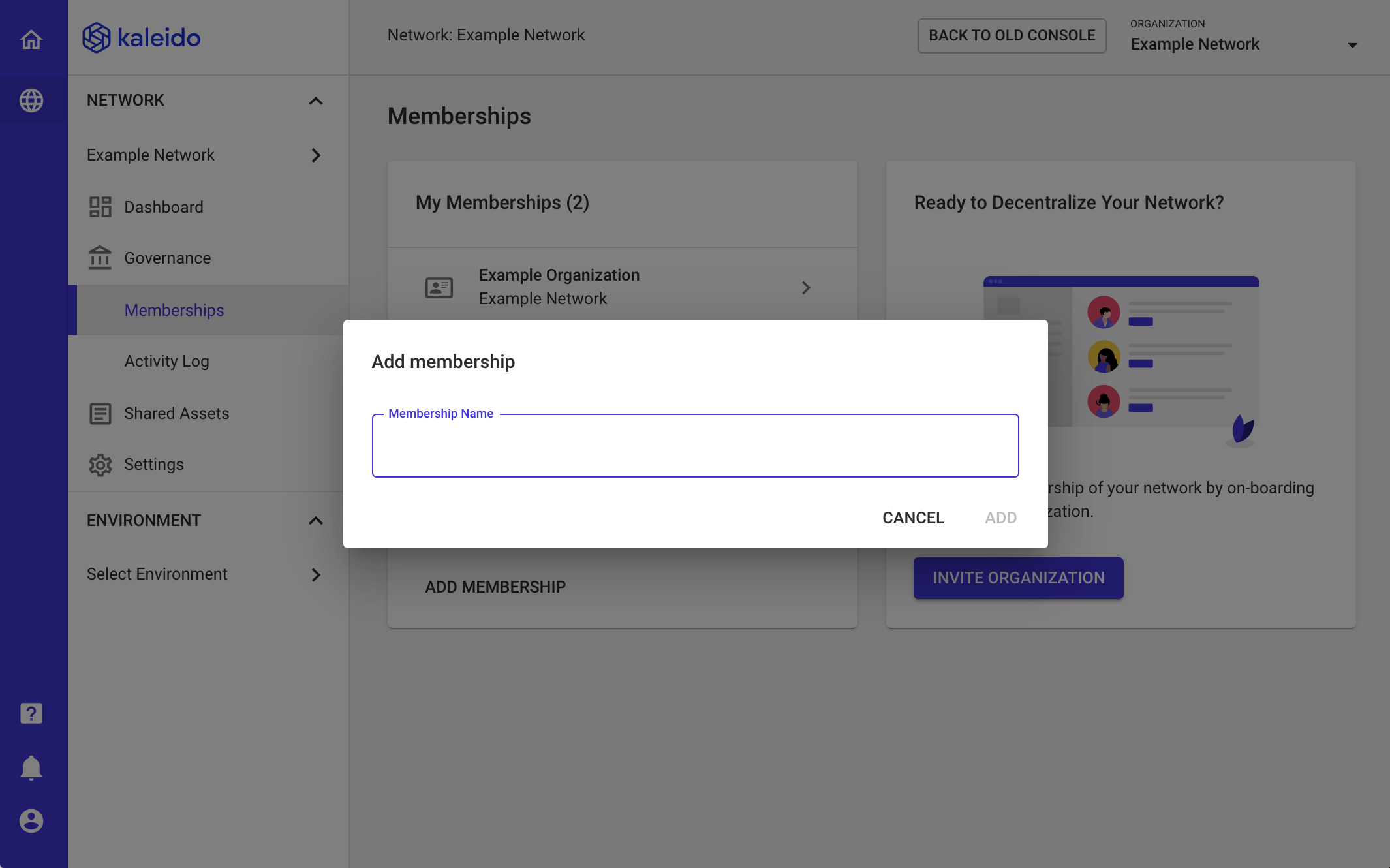
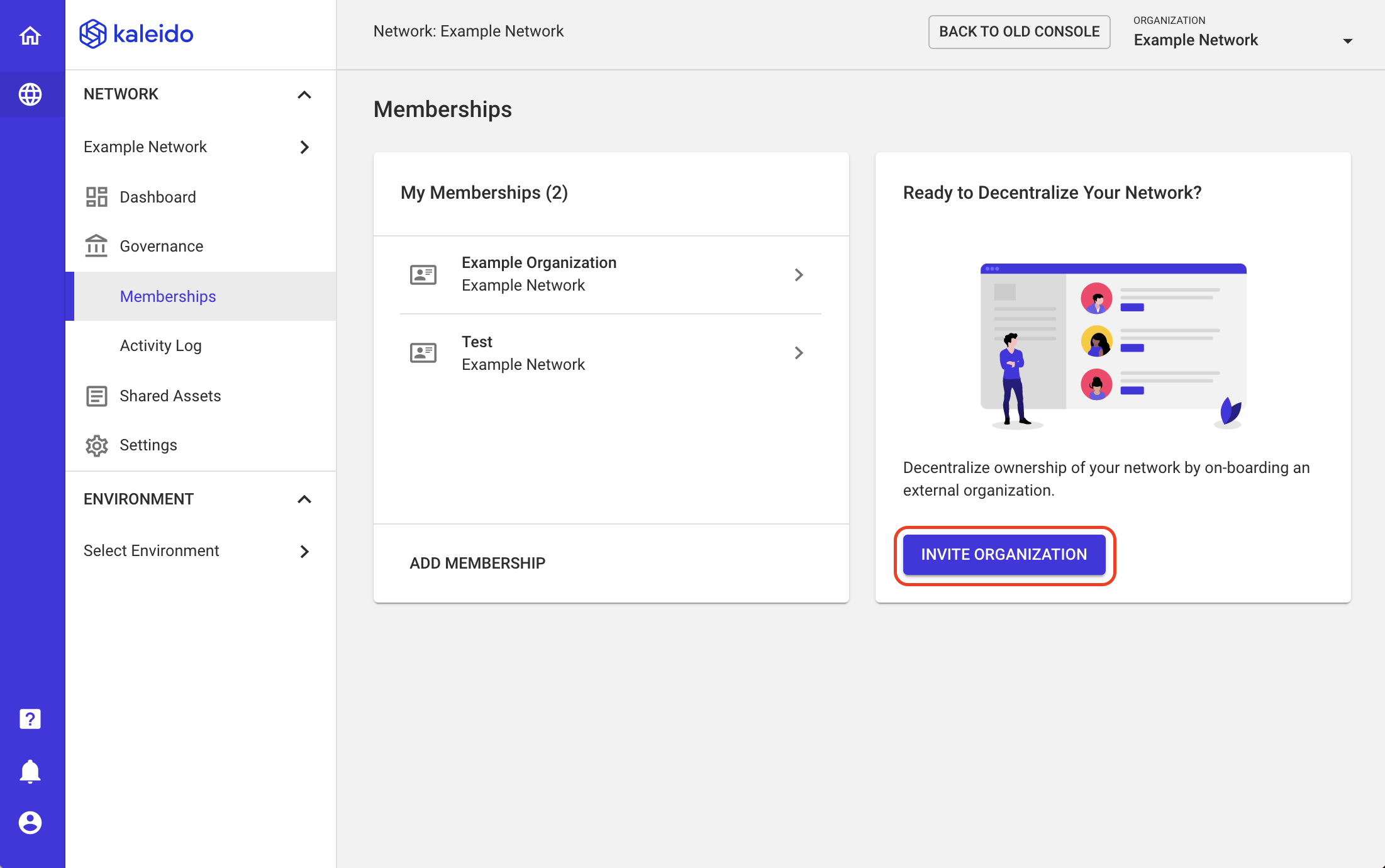
- To add a new membership, navigate to your consortium's governance page and select Add Membership.
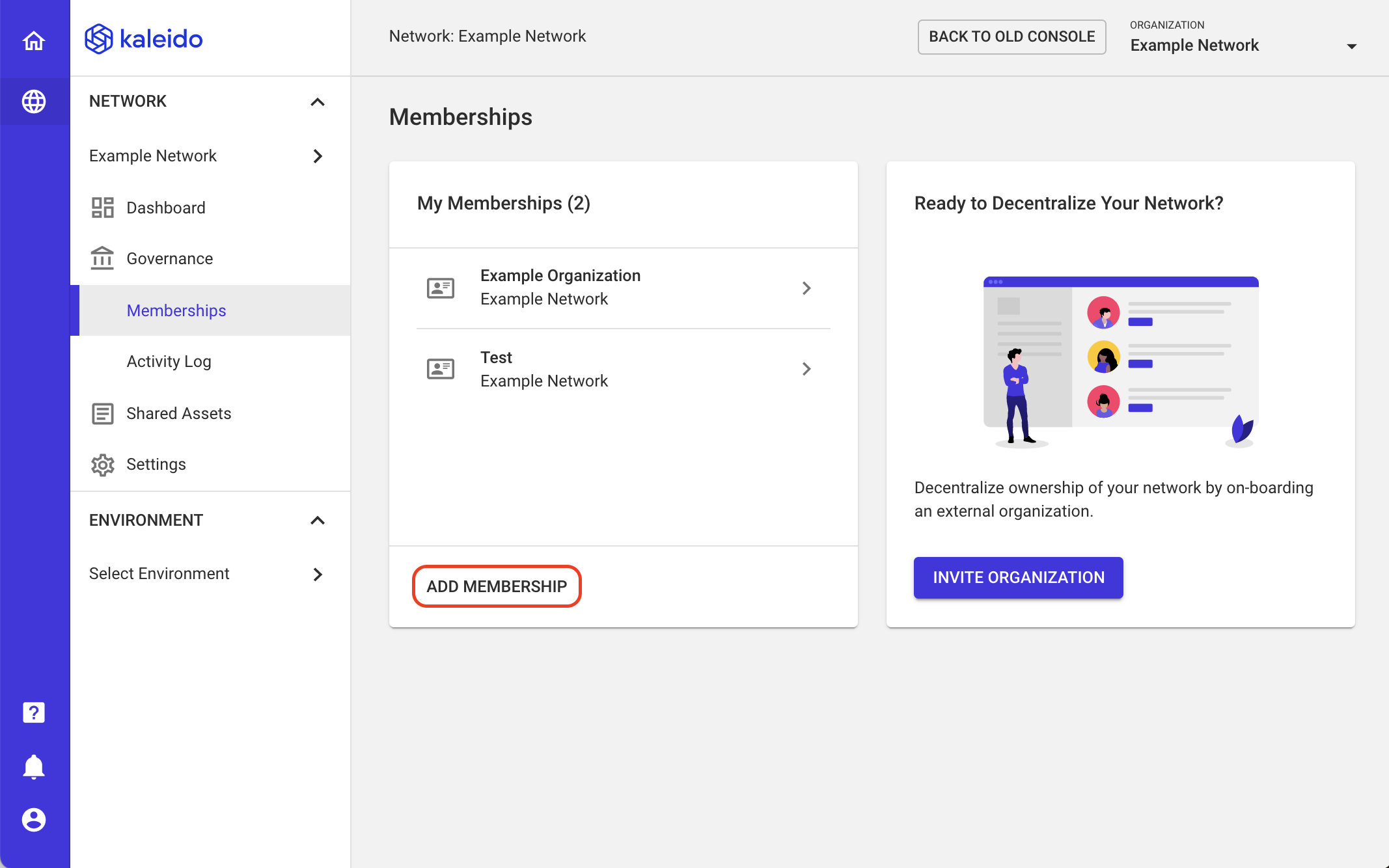
- Enter the participant's name (e.g.
Bank ABC) and click Add.
On-boarding an External Organization
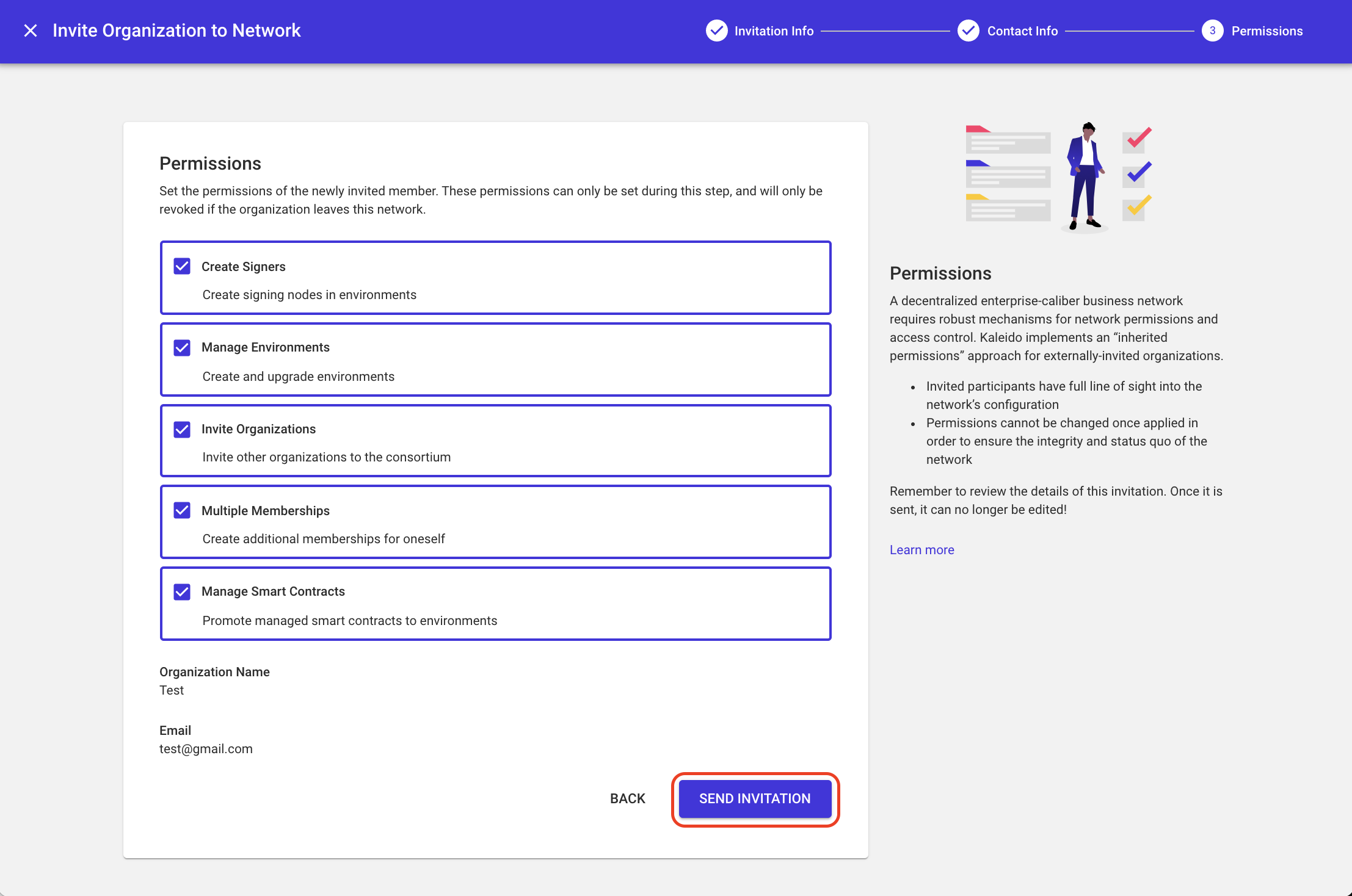
Decentralizing ownership of your consortium is made possible by onboarding external organizations. The founder of the consortium can accomplish this by issuing an invitation with embedded access control permissions. Any onboarded organization will be in sole control of their resources, services, and security credentials and will possess any ascribed permissions. To onboard an external organization follow these instructions:
NOTE: Only organizations on the Business or Enterprise subscription tier can extend/participate in a decentralized consortium. Only organizations on the Enterprise subscription tier can issue network permissions.
- Navigate to your consortia's governance page and select Invite Organization.
- A panel will appear describing the architectural transition of your consortia from centralized to decentralized. Click Next.
-
Enter the Organization Name of the external org and supply an admin email address.
-
Select or rescind permissions and choose Send Invitation.